As an experienced programmer, you’ve undoubtedly heard about root at localhost – a mysterious and powerful concept that seems to appear everywhere, from forum discussions to Stack Overflow questions. But what exactly does it mean? And, more importantly, how can you harness its potential to elevate your programming skills to new heights? If you’ve been searching for these answers, look no further! In this in-depth essay, we’ll dive into the secrets of root at localhost, exploring its purpose, potential risks, and practical uses in various programming scenarios. So buckle up and get ready for an exciting journey into the world of root at localhost.
Demystifying Root at Localhost
Root at localhost is typically synonymous with two intertwined concepts: administrative access and local server access. To fully grasp the topic, let’s break it down into its components.
1. Root Access:
Root access refers to the highest level of permissions available to a user within a system, such as changing configurations or modifying other users’ permissions. In UNIX-based systems, the “root” user possesses this supreme level of control, while in Windows, it’s the “Administrator” user.
2. Localhost:
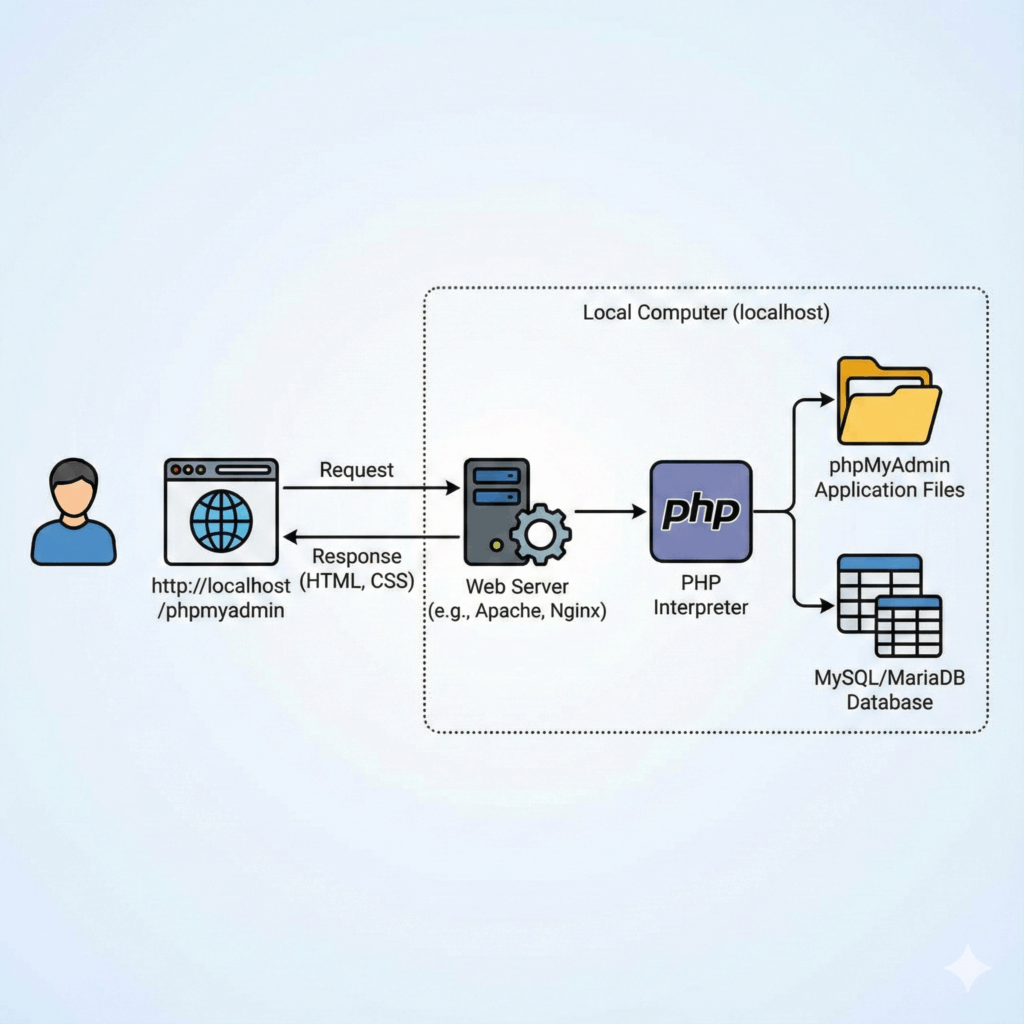
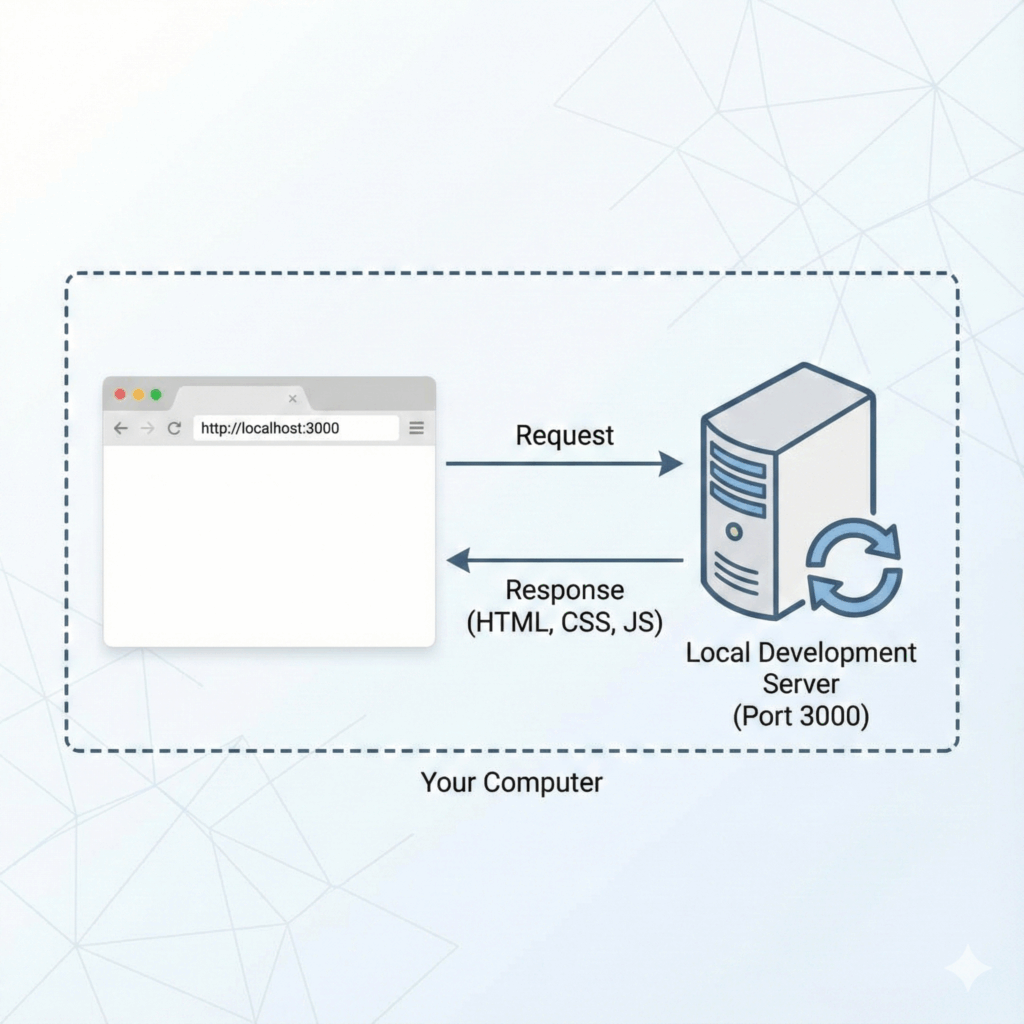
Localhost is a reserved domain name used to address the local machine, pointing to the IP address 127.0.0.1. Developers often use it for testing web applications on their machines before deploying to production servers.
With these definitions in mind, root at localhost simply refers to having administrative access on the local server environment. This powerful combination grants you full control over your machine, which can prove both beneficial and risky, as we’ll discuss further.
Security Implications and Risks
Operating as root at localhost can be a double-edged sword—it may provide unparalleled convenience, but it also exposes your system to potential security risks.
Key Risks:
– Accidental Damage: With full access to your system, mistakes made while working as the root user can have severe consequences, such as deleting critical files.
– Malware Vulnerability: Functioning as root makes your system more susceptible to malware, which could give attackers a backdoor into your system.
– Mitigating Measures: To reduce the risks associated with root at localhost, you can follow these best practices:
– Avoid working as the root user unless necessary. Instead, utilize other roles with limited permissions.
– Implement strong authentication methods, such as two-factor authentication, for root access.
– Regularly update your software to patch security vulnerabilities.
Practical Uses and Applications
While understanding root at localhost’s potential dangers is crucial, it’s equally important to appreciate its practical uses. Let’s examine some typical scenarios where root access on a local server can come in handy:
1. Web Application Development:
By setting up a local server environment, you can test and develop web applications without risking damage to live systems or exposing sensitive data.
2. System Administration:
As a system administrator, you’ll often need root access on local servers to manage system configurations, install critical updates, or troubleshoot issues.
3. Custom Software Deployment:
Root access is necessary when deploying custom-built software to local servers, ensuring compatibility, and minimizing the risk of unintended consequences within production environments.
Common Issues and Resolutions
Working with root at localhost can present challenges. Here are some common issues you might encounter and how to address them:
1. Permission Errors:
If you’re facing permission errors while accessing files or directories, double-check that you have the correct privileges. You may need to elevate your access level to root.
2. Connection Issues:
If you can’t connect to the local server via root at localhost, verify that the server is running, and firewalls aren’t blocking traffic.
3. Server Configuration Problems:
If your local server isn’t behaving as expected, carefully review its configuration settings. Consult the server’s documentation to ensure proper setup.
Top Tools for Working with Root at Localhost
To maximize your efficiency when working with root at localhost, consider taking advantage of these top tools specifically designed for local server environments:
– XAMPP: A popular, cross-platform, easy-to-install web server solution that includes Apache, MariaDB, PHP, and Perl.
– Docker: A platform for automating deployment, scaling, and management of containerized applications, perfect for local server environments.
– Vagrant: A tool for building and managing virtual machine environments, providing a consistent workflow across various platforms.
The Future of Root at Localhost
As technology evolves and new tools emerge, the landscape of root at localhost will undoubtedly change. However, at its core, the concept has always been about providing developers with control over their local environments, which will remain relevant in the foreseeable future. By staying informed about emerging technologies and best practices, you can wield the power of root at localhost responsibly and effectively to create world-class applications.
Now that you’ve reached the end of our deep dive into root at localhost, it’s time to take all the knowledge you’ve gained and apply it to your projects. Armed with this comprehensive understanding, you have the power to unlock the full potential of root access in your local server environment, elevating your programming skills and delivering remarkable results.
access EVERYTHING from your web browser!! (Linux and Windows Desktop, SSH) // Guacamole Install
Kubernetes Hacking: From Weak Applications to Cluster Control
How do I grant access to root on localhost?
To grant access to the root user on localhost, you need to modify the user privileges in your database management system. Here’s a general outline of the steps:
1. Log in to your database management system (e.g., MySQL, PostgreSQL) using an account with administrator privileges.
2. Select the database on which you want to grant root access.
3. Find the user ‘root’ in the list of users.
4. Edit the privileges for the root user. Depending on your specific database management system, the options might differ, but typically you’ll need to enable all global and database-specific privileges.
5. Save the changes and exit the user management interface. The root user should now have full access to the specified database on localhost.
Remember that granting root access can be risky, as it allows the user to perform any action on the specified database. Be cautious when granting these privileges and only do so when absolutely necessary.
What is the password for MySQL root localhost?
The password for MySQL root localhost is the one you set during the installation of MySQL on your system. If you have forgotten the password, you can reset it by following these steps:
1. Stop MySQL service: You will need to stop the MySQL service using your system’s services management tool or the command line.
2. Start MySQL with skip-grant-tables option: This allows you to access MySQL without a password. Open a command prompt and navigate to the MySQL installation folder (usually under Program Files). Run the following command:
mysqld --skip-grant-tables3. Open another command prompt and connect to the MySQL server by running:
mysql -u root4. Reset the root password:
FLUSH PRIVILEGES;
ALTER USER 'root'@'localhost' IDENTIFIED BY 'your_new_password';Replace “your_new_password” with your desired password.
5. Exit MySQL CLI by typing `exit` and hitting Enter.
6. Restart MySQL service: Close the first command prompt where the MySQL server is running (`mysqld –skip-grant-tables`) and restart the MySQL service using your system’s services management tool or the command line.
Now, you should be able to access MySQL root localhost using your newly set password.
How to enable root login in MySQL?
To enable root login in MySQL on localhost, follow these steps:
1. Open a terminal or command prompt.
2. Log in to MySQL using the current root user and password:
mysql -u root -p3. After successfully logging in, execute the following SQL command to enable root access from localhost:
GRANT ALL PRIVILEGES ON *.* TO 'root'@'localhost' IDENTIFIED BY 'your_password' WITH GRANT OPTION;Replace ‘your_password’ with your desired root password.
4. Reload the privileges to apply the changes:
FLUSH PRIVILEGES;5. Exit the MySQL shell by typing:
EXIT;Now, the root login is enabled for MySQL on localhost, and you can log in using the root credentials. Note that enabling root login can pose security risks, so make sure to follow best security practices and only use it when necessary.
Why is root access denied?
In the context of localhost, root access denied typically occurs because the system is designed to prevent unauthorized access to the most privileged user account, known as the “root” user. This account has full permissions to access, modify, and delete any file or system setting, which represents a significant security risk if mishandled.
There are a few common reasons why you might encounter a root access denied message:
1. Incorrect User: You may be logged in as a different user without sufficient privileges to perform the desired action.
2. Disabled Root User: The root account may be disabled by default, especially on systems running macOS or certain Linux distributions.
3. Wrong Password: You may have entered the incorrect password when attempting to authenticate as the root user.
To resolve this issue, ensure that you have the correct level of permissions and the appropriate credentials to perform the actions you’re trying to execute. Additionally, consider using the sudo command (on Unix-based systems) for temporary root access, which provides greater security and accountability.
What are the common scenarios for encountering the “root at localhost” user in localhost environments?
There are several common scenarios in which you might encounter the “root at localhost” user in localhost environments:
1. MySQL/MariaDB installation: During the installation process of MySQL or MariaDB, you are required to set up a root user that has complete access to your database. This user is often referred to as “root at localhost” since it can only access the databases from the local machine.
2. Secured database administration: When managing a database on a localhost environment, you might use the root user to create new users, grant privileges, or make other administrative changes. The root user has the highest privileges, so it is essential to protect its access.
3. Local development and testing: When developing web applications or server-side software on a localhost environment, developers often use the root user to manage databases and perform operations, such as creating tables, inserting data, or querying databases.
4. System administration: In some instances, you might encounter the “root at localhost” user when managing the local system or installing/configuring some software packages. Root user in Linux/Unix systems holds full control over the system configuration, file system, and installed applications.
5. Troubleshooting issues: Sometimes, when facing issues with applications or services running on your local system, you may need to use the root user to identify the problems, analyze logs, or modify configuration files.
Remember that using the root user comes with great responsibility, as any mistake can lead to unintended consequences. It is always best practice to limit root usage and rely on lower-privileged users for everyday tasks.
How can one manage and maintain security when using the “root at localhost” user in a local development setup?
To manage and maintain security when using the “root at localhost” user in a local development setup, follow these best practices:
1. Use strong passwords: Always use a strong and unique password for the root user. This makes it difficult for unauthorized users to gain access.
2. Limit root access: Restrict root access to specific IP addresses or limit access to only the localhost. This ensures that the root user can only be accessed from trusted sources.
3. Monitor log files: Regularly monitor your server’s log files for any suspicious activity or unauthorized access attempts. This helps you stay aware of potential security threats.
4. Keep software up-to-date: Always update your server software, applications, and dependencies to their latest versions. Outdated software may contain security vulnerabilities that can be exploited.
5. Create non-root users: Create non-root users with limited privileges for everyday tasks. This minimizes the risk of a security breach caused by a compromised root account.
6. Disable remote root login: If your server allows remote logins, disable the remote login capability for the root user. This adds an extra layer of security to your server.
7. Implement Two-Factor Authentication (2FA): Use 2FA to protect the root user’s login credentials, ensuring that an additional layer of authentication is required before granting access.
8. Follow the principle of least privilege: Grant users and applications the minimum level of access they need to perform their tasks. This reduces the risk of unauthorized access and potential damage.
9. Backup your data: Regularly backup your data, configurations, and applications to ensure they are protected in case of accidental deletion, hardware failure, or other unexpected events.
10. Use security tools and audits: Use security tools like intrusion detection systems (IDS), firewalls, and regular security audits to monitor and protect your server against potential threats.
What are the recommended best practices for handling permissions and password management for the “root at localhost” user while working on a localhost environment?
It is essential to manage permissions and password security for the “root at localhost” user while working on a localhost environment. Here are some recommended best practices:
1. Strong Passwords: Use a long, unique, and complex password for the root user. It should contain a mix of letters, numbers, and special characters. Avoid using common phrases or easily guessable passwords.
2. Password Manager: Employ a reputable password manager to store your root password securely. This will help you remember complex passwords without having to write them down.
3. Restrict Root Access: Limit the number of users who have access to the root account. Grant access only to those who need it for their tasks, and revoke it immediately when it is no longer required.
4. Use sudo: Instead of logging in as the root user to perform administrative tasks, use the “sudo” command. This allows you to execute commands with root privileges without exposing the root password.
5. Regularly Update Passwords: Change the root password on a regular basis. Using an updated password helps prevent unauthorized access.
6. Monitor Access Logs: Keep an eye on access logs for any suspicious activity related to the root account. Investigate any irregularities immediately to ensure your system remains secure.
7. Implement Two-Factor Authentication (2FA): If possible, enable 2FA for your root account. This adds an extra layer of security, requiring additional verification before providing access.
By following these best practices, you can help maintain the security of your localhost environment while managing permissions and password security for the “root at localhost” user.